Stop drowning in alerts your team doesn’t have time to investigate
Most alerts aren’t emergencies. But figuring out which ones are takes just as long.
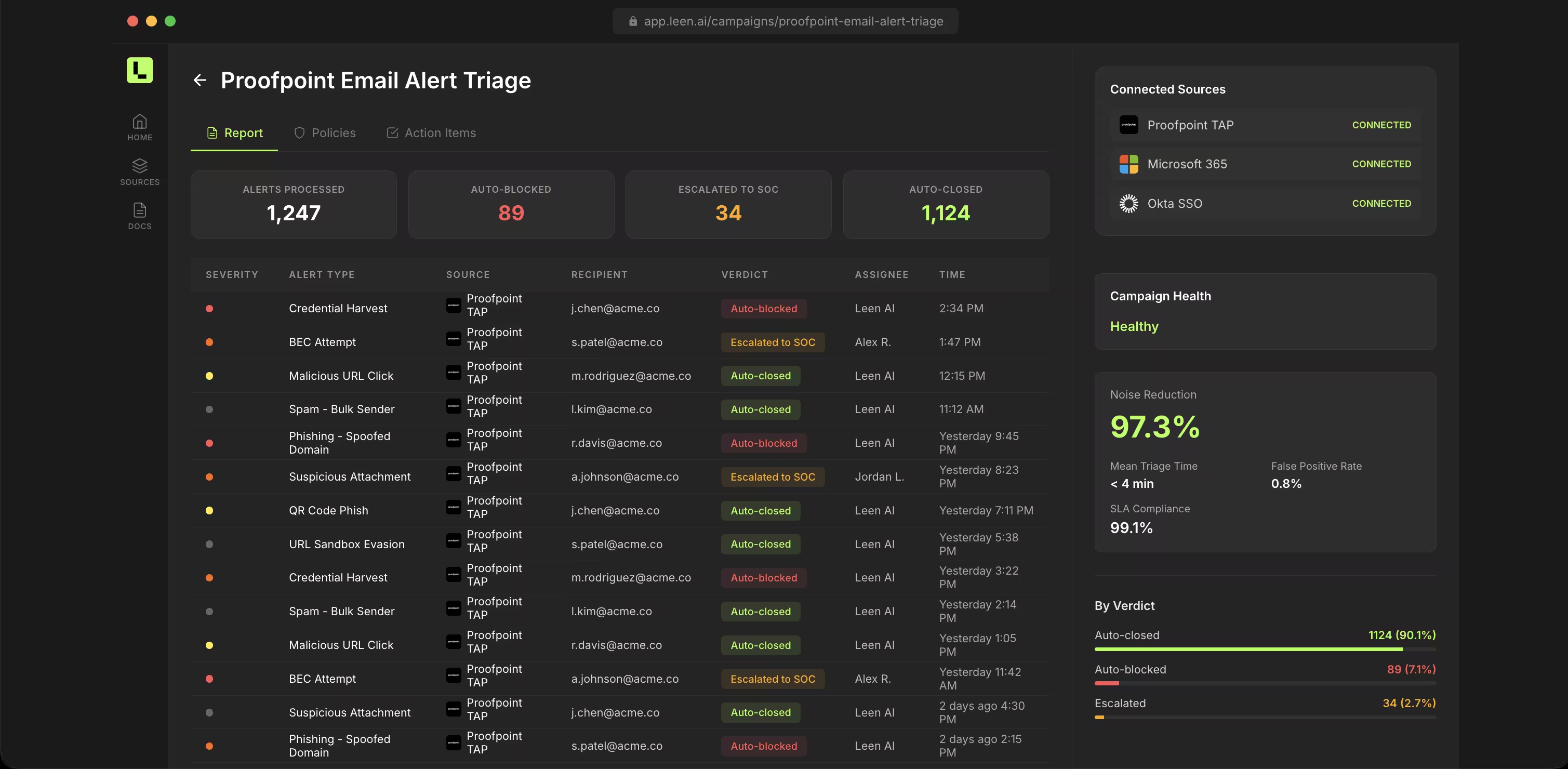
Hundreds of alerts a day. Most informational, many duplicates, a few genuinely urgent. Each one takes 20 minutes to investigate: check the asset, look up the owner, review activity, decide whether to escalate. Your team spends most of its time confirming alerts are benign.
Intelligent triage that filters the noise
Cross-tool correlation
CrowdStrike alert + AWS config change + suspicious Okta login = a different story than any one signal alone.
Context-enriched investigation
Every alert auto-enriched with asset context, ownership, history, and business criticality. Full picture, no tool-pivoting.
Smart routing
Cloud alerts to the cloud team. Access anomalies to the identity team. No more shared queues.
Noise reduction
Leen learns which patterns are benign in your environment and deprioritizes them based on your policies.
Multi-source correlation
Combine signals from EDR, cloud, identity, and network tools into unified investigation threads.
Historical pattern matching
Leen remembers past investigations and applies that knowledge to new alerts.
Escalation policies
Define when and how alerts escalate. Leen handles routing and follow-up.
What your team gets
Less noise, more signal
Time on real threats, not confirming false positives.
Faster response
Real alerts investigated immediately with full context.
Nothing falls through
Every alert tracked and resolved. No more “I thought someone else was looking at that.”


