Your security team just got a lot bigger
Leen agents connect your security tools, normalize the data, and run end-to-end campaigns - from finding the problem to proving it's fixed.
Security teams shouldn’t spend their days copying data between tools
Fifteen tools. Five scanners. Every investigation is the same ritual: open a finding, pivot to the asset inventory, check the owner in Okta, look up business context, figure out who gets the ticket. Meanwhile, the backlog grows, SLAs slip, and auditors want evidence you have to compile by hand.
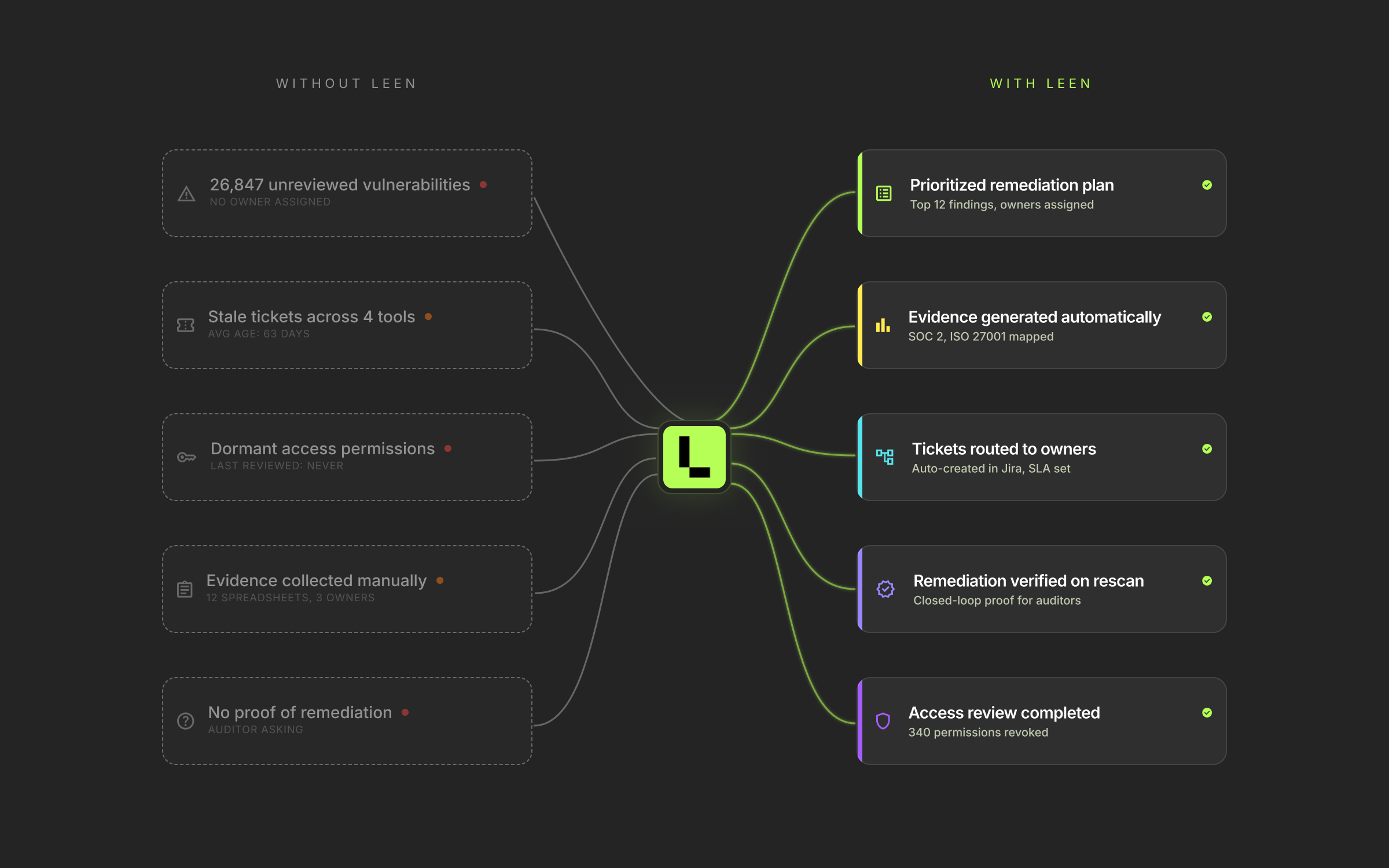
Without Leen
Findings in one tool.
Assets in another.
Ownership in a spreadsheet.
Your team spends days stitching data together before any remediation even starts.
Assets in another.
Ownership in a spreadsheet.
Your team spends days stitching data together before any remediation even starts.
With Leen
One conversation: "Run our quarterly cloud posture campaign."
Leen normalizes the data, enriches findings with business context, routes to owners, follows up, and proves completion.
Leen normalizes the data, enriches findings with business context, routes to owners, follows up, and proves completion.
What if your tools could actually work together?
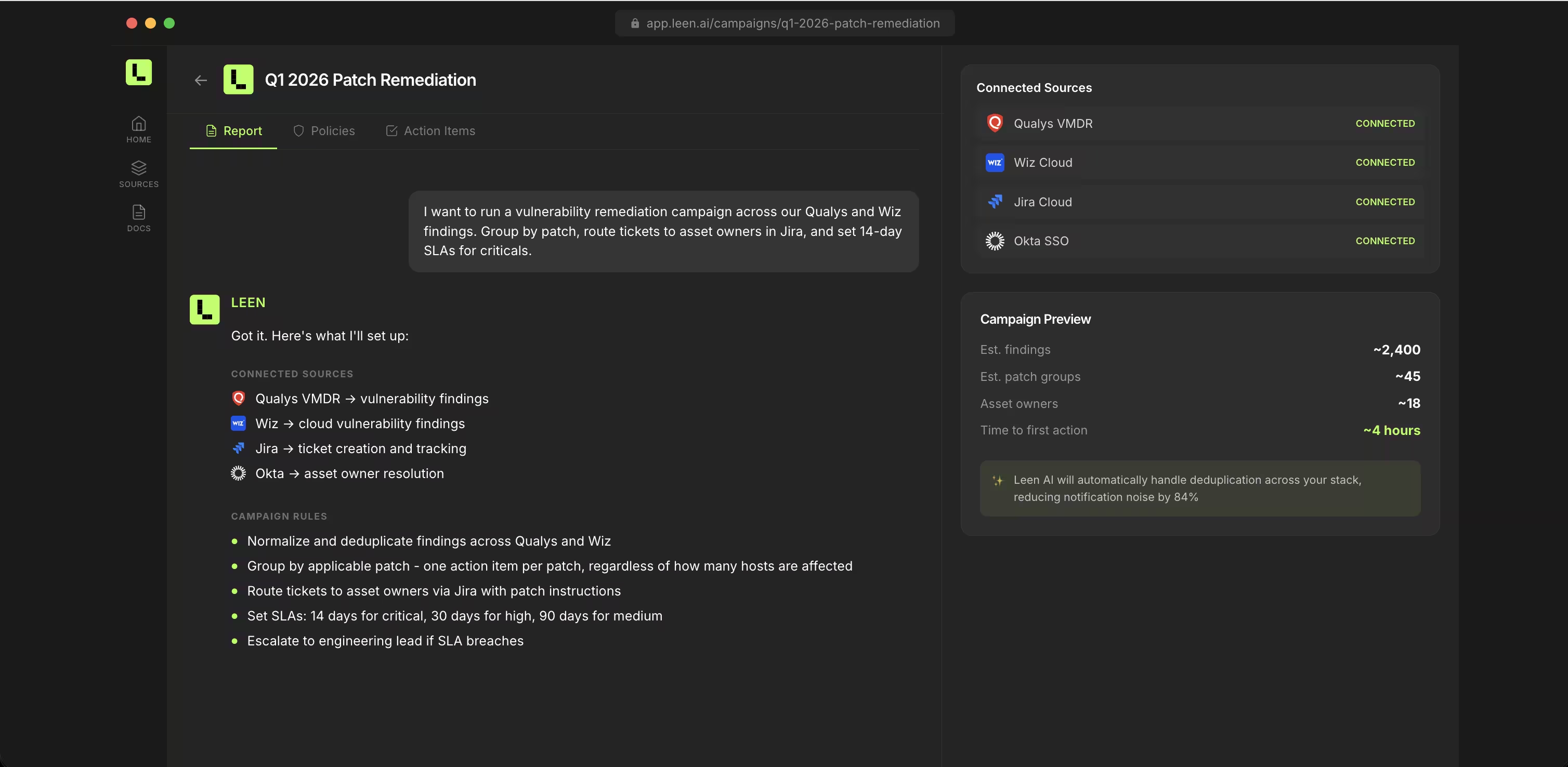
Leen connects your security and business applications, builds a unified picture of your environment, and gives your team an AI collaborator that does real work, not just generates dashboards.Step 1
Tell Leen what you’re working on
Vulnerability management, access reviews, or audit prep. Define your security objective and Leen connects to the relevant tools to make it happen.
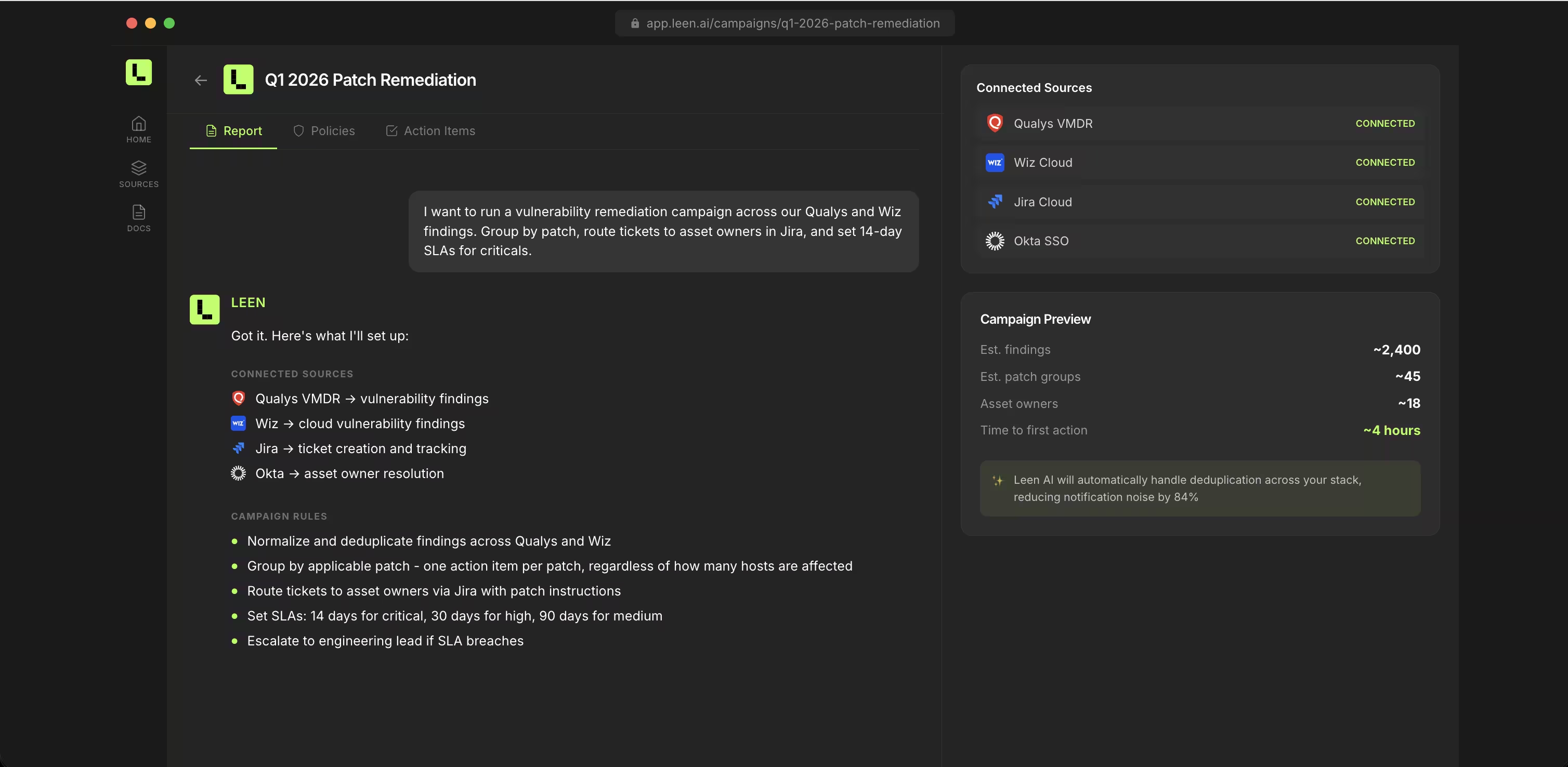
Step 2
Leen investigates and builds a plan
Cross-references your scanners, identity providers, cloud platforms, and ITSM tools. Presents a prioritized action plan.
Step 3
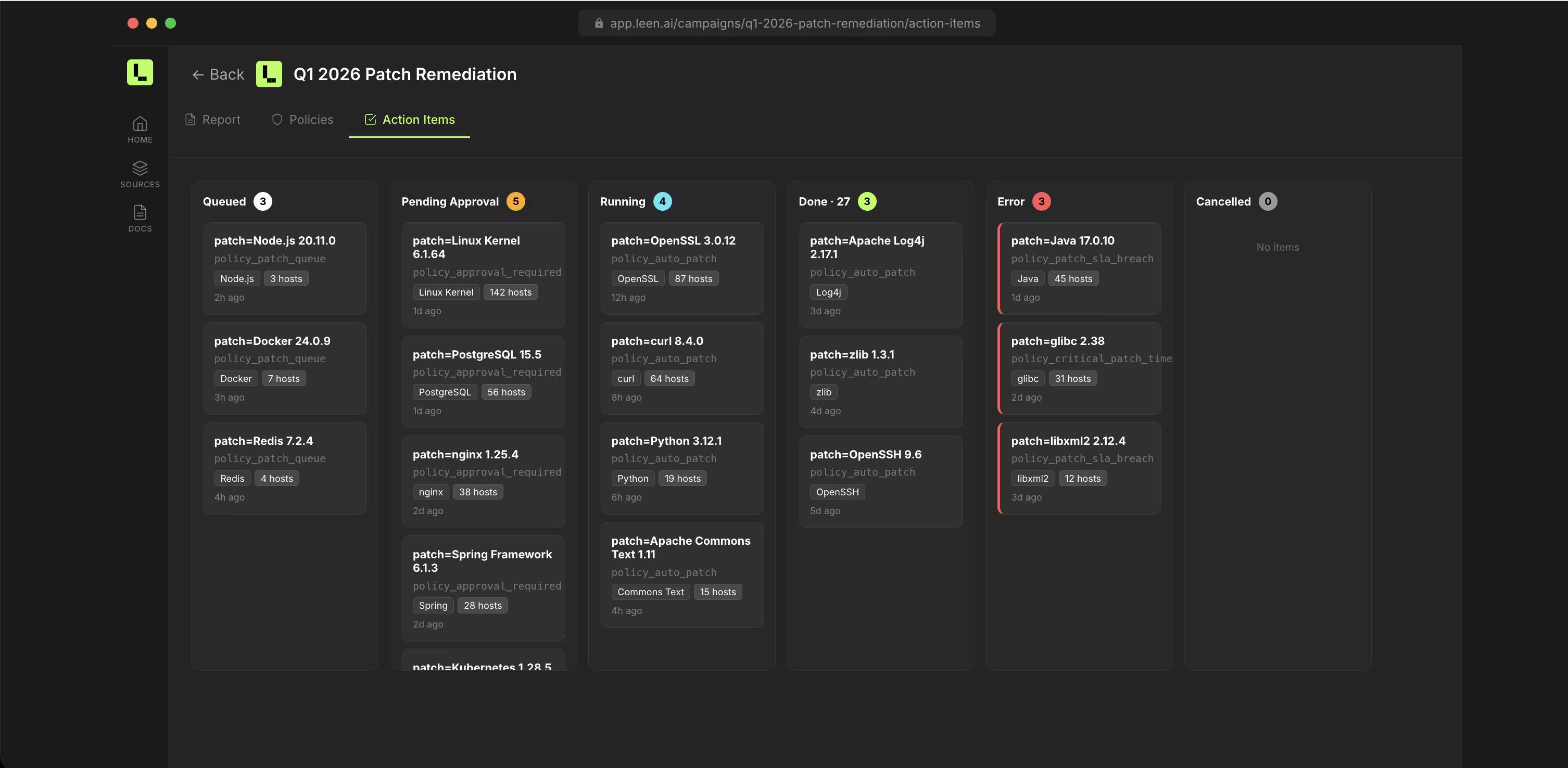
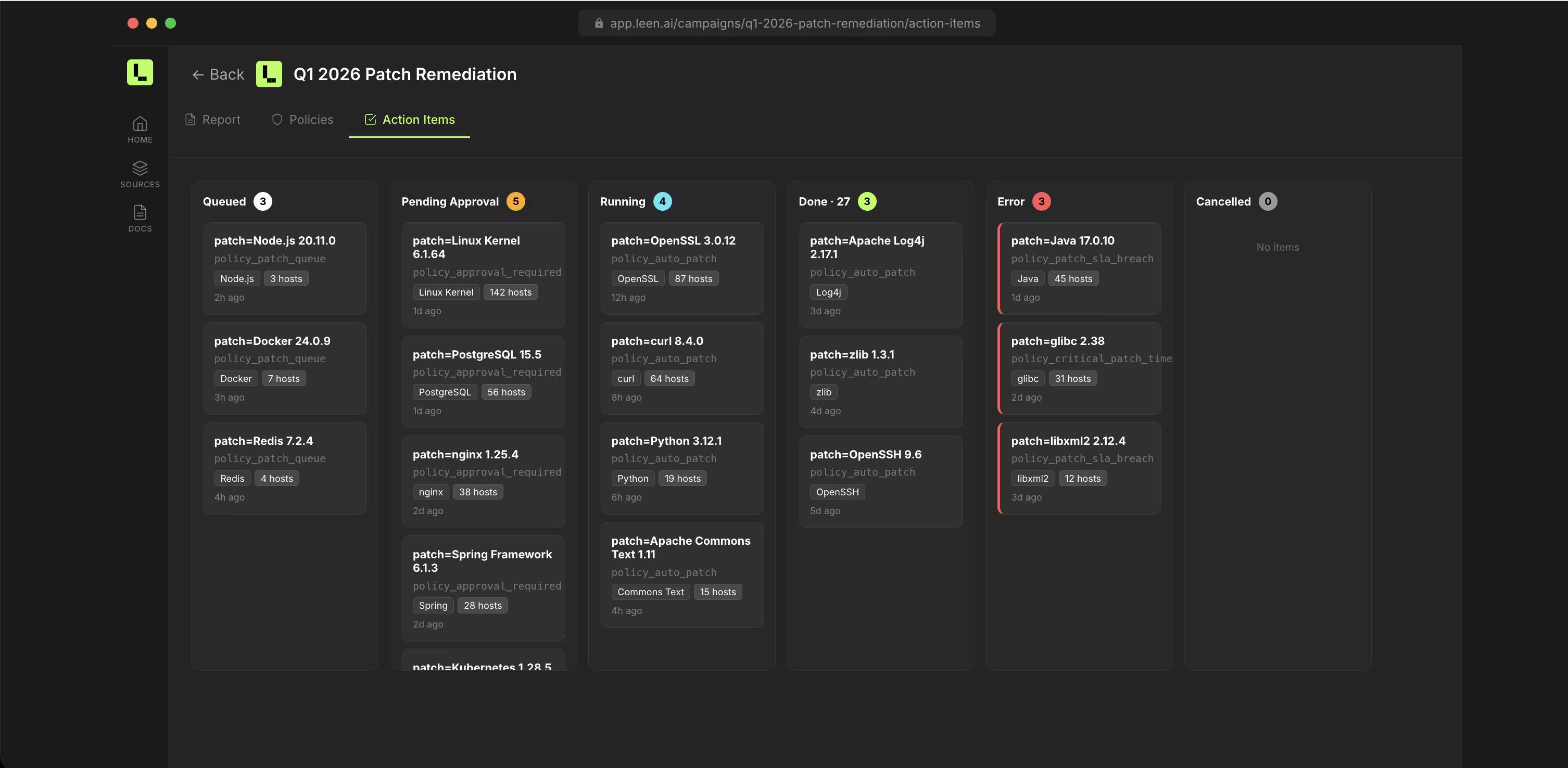
Approve it and move on
Leen creates tickets, follows up with owners, escalates overdue items, and validates fixes- all without pulling your team out of Slack. Security engineers manage programs, check status, and adjust policies right from the tools they already use. Asset owners and engineers get pinged in Slack with exactly what they need to do.
Use cases
One platform across your security programs
One agentic platform that works across your programs
What changes with Leen
4
0
9
4
3
7
8
6
4
1
5
4
3
2
7
8
0
4
2
0
+
From spreadsheet to system
Remediation tracked end-to-end. Every finding, every owner, every SLA in one place instead of scattered across Jira, Slack, and Google Sheets.
4
0
9
4
3
7
8
6
4
1
5
4
3
2
7
8
0
4
2
0
+
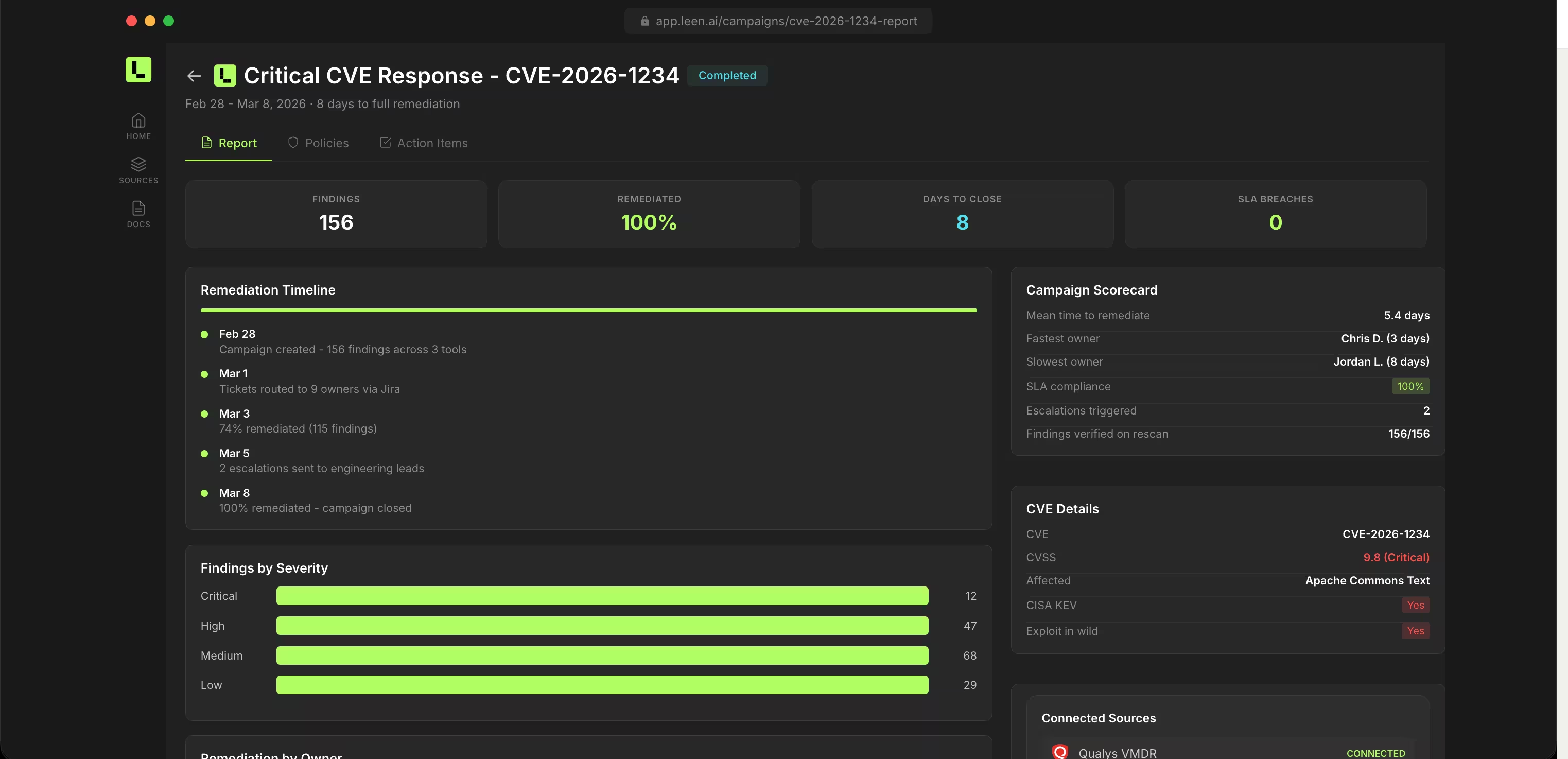
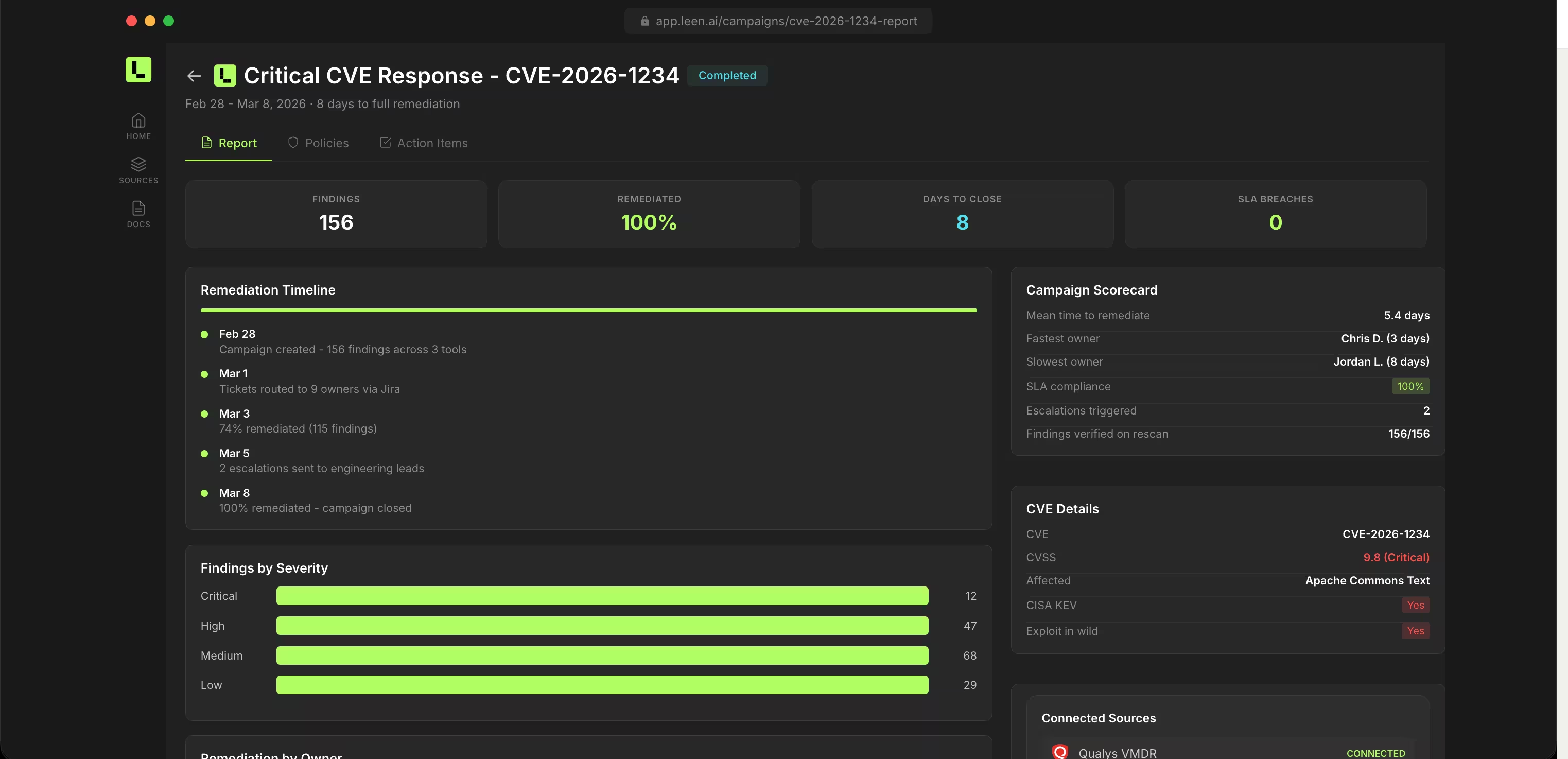
From finding to fix
Leen doesn't stop at detection or prioritization. Findings get routed, followed up, validated, and closed without your team chasing tickets.
4
0
9
4
3
7
8
6
4
9
8
4
3
2
7
8
0
4
2
0
%
From quarterly scramble to continuous proof
Evidence generated as a byproduct of real remediation. Always audit-ready, not assembling screenshots the week before.








Let's talk
See what Leen can do with your stack
No pitch deck. No questionnaire. Bring your tool list, we'll show you what's possible.




